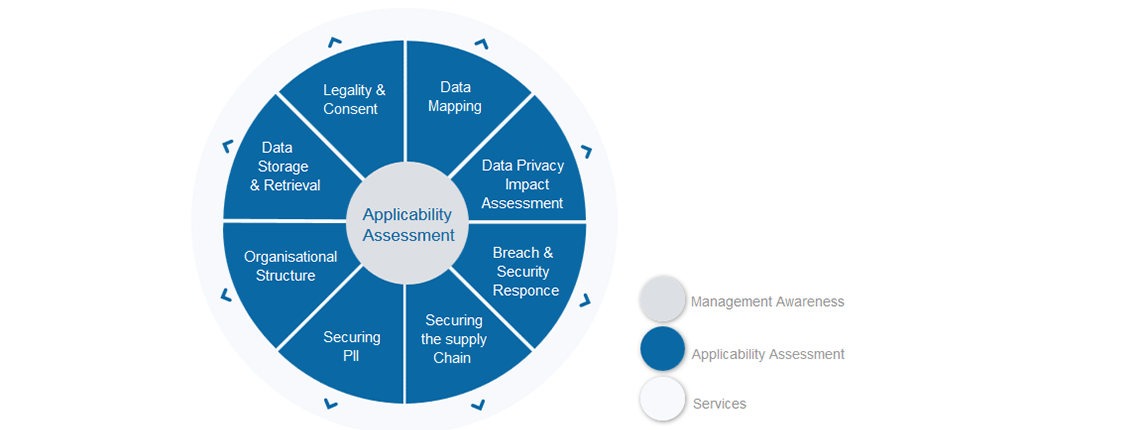
This is week five of the GDPR walkthrough – you’re more than halfway there and already covered Legality & Consent, Data Mapping, DPIAs and Breach & Security Responses. This week we will step back from our organisations and make sure that the partners you rely on are looking after your data and not exposing you to breaches, fines and all that nastiness.
What are the expectations?
GDPR calls out subcontracting of processing specifically and while there is no objection to that model, direct compliance obligations are imposed on both controllers and processors, and both controllers and processors will face direct enforcement and penalties if they do not comply. If your organisation acts as both the controller and processor then compliance is within your own control, however, if you use third parties to process data, you need to ensure that they are compliant or you will both suffer.
How to secure the supply chain
The first thing to establish of course is whether there are third parties involved in the processing of data. This should have become evident in week two when you performed the Data Mapping exercise and will include any company involved in the processing of data that you control. That could be external suppliers who work with your PII, who host PII for you, who provide hosting or backup services, or in any other way have access to where the PII is stored. If the third party could in any way access or expose PII controlled by your organisation, then it must be considered.
Once you have the comprehensive list of third parties it is a matter of validating how they handle the data and reflecting that contractually. The questions to explore are:
- Does the third party meet GDPR requirements? Can they prove it?
- Is there any further outsourcing involved that you have not considered? Confirm that the third party has no additional downstream companies who could access your organisation’s data
- Is security adhered to in the third party? For example, is the third party ISO27001 certified? What are the breach reporting processes?
- Remember to validate the transfer of data between your organisation and the third party, there could be weaknesses there
Once you are comfortable that there is no risk in the relationship, it needs to be ratified legally. Now is when you’ll need to get the contracts team to amend the contract – if you don’t have a team, contact the third party and explain what is required (namely a clause that they will adhere to GDPR). There is going to be a lot of this happening in the lead up to May 2018, so it shouldn’t come as a surprise to any service provider. However, the bad news is there is a risk that the additional costs to meet the increased compliance obligations when it comes to renewing the contract.
Summary of Securing the Supply Chain
This week should be a reasonably straightforward exercise building on the work you did in earlier weeks. In a nutshell, you need to find out exactly who can access your PII – anyone from outsourced payroll providers to hosting organisations. Once you have that you need to verify the security – don’t be shy to ask probing questions or evidence. If anything goes wrong you will be asked those questions by the regulator, so better to do it now. Finally amend the contract so that the third party has an obligation to continue to secure and meet your high standards. So, an easy task, but it could be time consuming and not one to leave until April 2018!
Next week – six of eight:
Next week we will focus on Securing the PII processed by your organisation.
Any questions contact about this week or any other GDPR topic, please contact graeme.riley@intersyscompliance.com
Graeme Riley is an experienced Global CIO with extensive experience in IT Security and Data Protection. He is currently a Director at Intersys Compliance Ltd.


