This is week two of our 8 week GDPR walkthrough – hopefully having completed week one, you managed to look at the data your organisation holds and understand the changes that your organisation needs to make around consent to comply with GDPR.
This week is quite straightforward – but it will be time consuming. The objective is to get to the next level of detail on the data held through an exercise called ‘Data Mapping’ which is a GDPR requirement – Article 30 for anyone who is interested. Data Mapping will document the lifecycle of the Personal Identifiable Information (PII) through your organisation – who owns the data, where it is held and importantly and who can access it.
Having this information documented will help your organisation to not just understand the vulnerabilities, but also to respond more efficiently to data subject requests as you will know where their data is processed and held.
How to Map the Data
It is likely that the Data Mapping will involve quite a few team representatives from around the organisation, so the importance of the exercise will need to be stressed to get them along. Essentially what you are trying to achieve is:
- Understand the PII being held and handled by the organisation – start from the collection of the data
- Where is it stored? (location of the systems processing and storing the data – remember backups, tapes, audio recordings etc.)
- Who ‘owns’ or is accountable for the data?
- Who can access the data?
- Remember to consider third parties and system interfaces as part of the process flow
A good way to start the exercise is with a whiteboard. Get everyone to contribute to what data they hold and what systems they use – for example HR will hold sensitive employee data, staff performance information and even candidate CV. Sales will have CRM data containing sensitive data. Operations may have bank account details and credit cards. Get it all down on paper and then find an owner. You should also understand where this information is passed from system to system as part of the process flow and start to look for vulnerabilities.
At the end of the Data Mapping exercise you will have a lot of information and more than likely, a load of actions to look at. There will be surprises as well – did anyone ask for consent before recording customer’s wives’ birthdays in the CRM system? HR may think they are the only ones with access to their data, but did they know that IT are able to view the database where it is kept, or another team can access it through another system? Did Operations know that their data is being used by Sales to cross sell products?
Importantly you will now know all the PII held in the organisation, where it is, who owns it and who can access it. Once you have that information you are in a strong position to start implementing controls and planning what needs to be done to secure the data that you now know you are dealing with.
Summary of Data Mapping
Data Mapping allows you to understand what data you have, where it is and who can access it. It is fundamental to be able to plan the GDPR project, but also to give your organisation the holistic picture of PII, owners and access. The quality of the Data Mapping work will ultimately dictate your compliance with GDPR. If you don’t know about data, you can’t secure it. In summary, here’s what you need to do:
- Try to get all the relevant team members in one room for a brainstorming exercise
- Document what PII is collected, where it is held, who owns it and who has access to it
- Look for system or process weaknesses around access control, transfers to unsecured systems, 3rd parties accessing data
- Compile a flow (graphic or otherwise) of data in, around and eventually out of your organisation
- Make sure you get sign-off from those involved – if they are not giving you the full picture, then you can’t be expected to secure the data, so they need to put their name to it
Next week – three of eight:
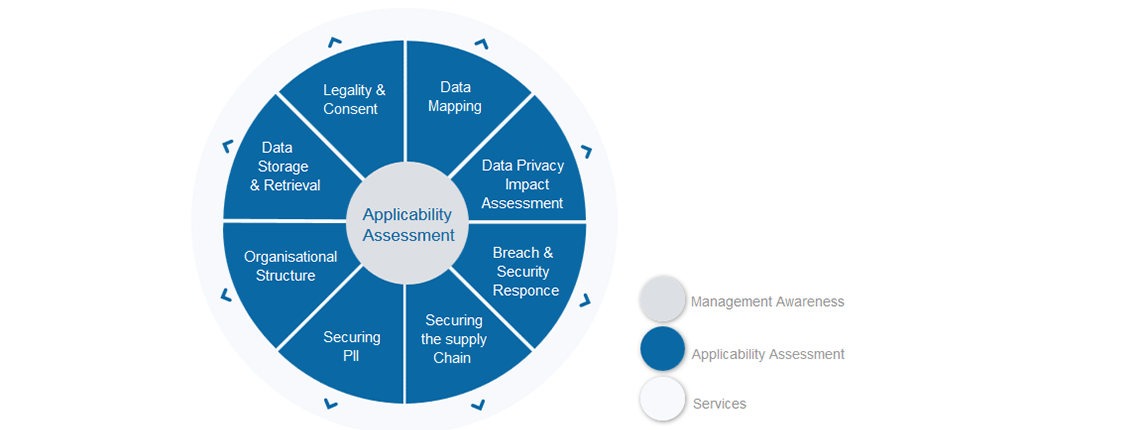
Next week we will focus on completing a Data Privacy Impact Assessment (DPIA) something which is mandated by GDPR to identify and address privacy risks. Any questions contact about this week or any other GDPR topic, please contact graeme.riley@intersyscompliance.com
Any questions about this article or any other GDPR topic, please contact:
graeme.riley@intersyscompliance.com
Graeme Riley is an experienced Global CIO with extensive experience in IT Security and Data Protection. He is currently a Director at Intersys Compliance Ltd.


