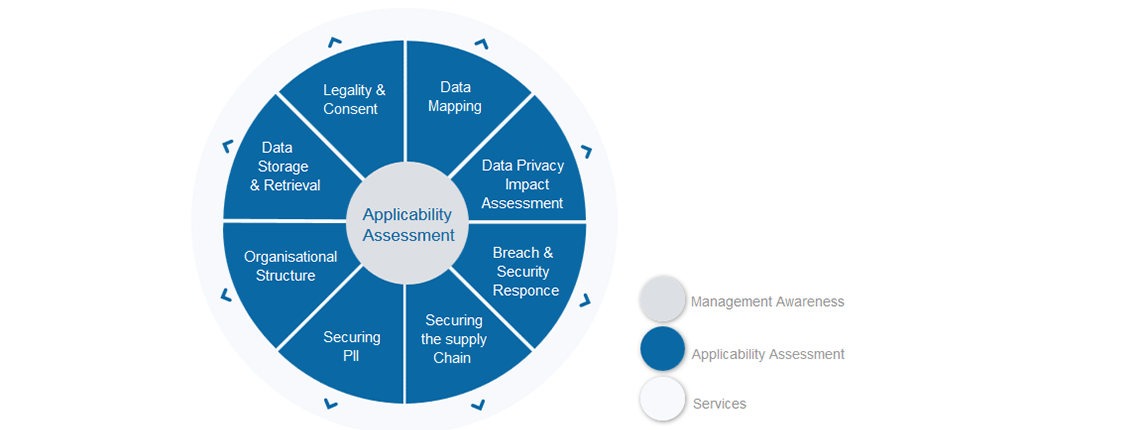
This is week three of the GDPR walkthrough – if you have followed week one and week two, you should now understand the data that your organisation is holding, where it is, who is responsible for it and whether you have consent from the Data Subjects to process it. That is a great start to shaping and implementing your compliance project.
This week is another important lesson that needs to be understood and a process implemented to accommodate it – the subject is that of the Data Protection Impact Assessment (DPIA). GDPR places the responsibility of running DPIAs with the controller to evaluate the details and levels of risk threatening Personal Identifiable Information (PII). If the risk from the assessment is shown to be high, then GDPR expects the controller to consult with the Supervisory Authority prior to processing.
What is a DPIA?
A DPIA is a fairly straightforward assessment of risk employed when something is going to change. That change could be a project which uses PII in a new way, implements a new processing automation or processes for sharing data are changed. The concept is that ahead of such a change, a DPIA is carried out to evaluate what data is being placed at risk, what controls need to be employed, or if the proposed solution is workable. There are far too many examples of data breaches being triggered by changes, technical or otherwise, that did not test or evaluate the possible consequences. This is exactly what the DPIA process is trying to avoid.
How is a DPIA run?
The most important first step is to recognise the need for a DPIA to be carried out. It makes sense to build the DPIA into another Project Management process so that upon project initiation, the requirement to run a DPIA is considered. Once it is recognised as required, then there are four keys steps:
1. Document the information flow that is being modified. This could be the PII database being transferred, the PII being processed differently or a new technology being implemented that touches the PII in some way
2. Once you have established how the information flow is being placed at risk, the specifics of how need to be understood. So, in step 1 if you established that records are going to be transferred to a new IT system, in step 2 you need to understand how that causes a privacy risk, perhaps by potentially causing a corruption, an unintentional transmission or a data loss
3. Now you understand the specifics of the risk, you can identify mitigation that could potentially be used to reduce the risk identified – the mitigating actions
4. Lastly, you need acceptance and sign-off before proceeding. As noted earlier, if the risk is significant enough, you need to consult with the Supervisory Authority before making the change. If something goes wrong and some or all of the above steps were not followed or cannot be demonstrated, then penalties will be more severe
Who runs the DPIA?
If one exists in your organisation, it is the job of the Data Protection Officer (DPO) to carry out the DPIA. If there is no DPO in the organisation, then there needs to be a process or tools created to allow non-experts to work through the DPIA process effectively.
Summary of Data Protection Impact Assessment
Running a DPIA ahead of making any changes that could jeopardise the privacy of data is required as part of the GDPR. The assessment should be integrated into existing Project Management processes and be flexible enough to be able to cover risks in processes, people or technological changes. The output of the DPIA is a documented analysis of the changes being made, the risks and the mitigating actions which should be accepted and signed ahead of the change. If the impact of the change is viewed to be of high enough risk to PII, then the Supervisory Authority needs to be consulted with ahead of any implementation.
Next week – four of eight:
Next week we will focus on Breach & Security Response and ensure the new touchpoints required by GDPR are incorporated into your procedures.
If you need some external support to get some momentum or just to get off on the right foot, drop Intersys Compliance a note and we’ll be happy to provide you a helping hand.
Any questions about this week or any other GDPR topic, please contact graeme.riley@intersyscompliance.com
Graeme Riley is an experienced Global CIO with extensive experience in IT Security and Data Protection. He is currently a Director at Intersys Compliance Ltd.


