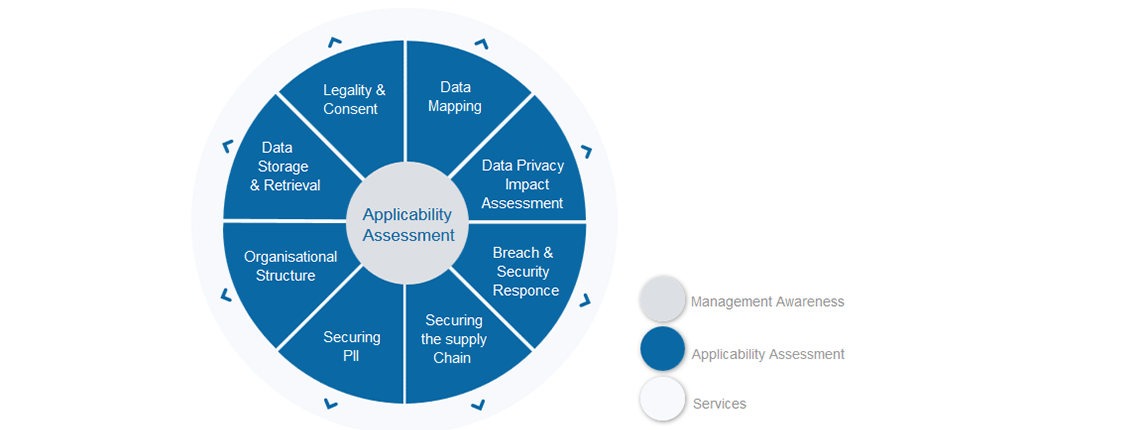
This is week six of the GDPR walkthrough and we have covered a lot so far. What we will be doing from now until completing the 8 weeks is looking at the steps your organisation needs to take to secure the data you hold, any changes or organisational arrangements that you need to consider and lastly the new data retrieval obligations you need to be ready for.
So, let’s start with securing the PII you hold. The 6th principle of GDPR is that organisations must ensure ‘appropriate’ security is in place including protection against unlawful processing, loss or damage and technical and organisation measures must be in place. Obviously, the security of the data is fundamental – the quickest way to get noticed by the Supervisory Authority and earn yourself a healthy fine is to suffer a data breach impacting PII. If your organisation is so secure that you can never suffer a data breach, then implementing GDPR will be a quick process. But few of us are willing to believe that, so this week will look at what you should be reviewing and implementing to keep things right.
What are the expectations?
The practical interpretation of the 6th principle is that you need to take appropriate measures against the data that you are processing – so if it is internal HR data that you are using, you may find a simple way of securing or isolating that out of harm’s way. But if you are actively processing sensitive medical information then it is a very different matter and you will be expected to design and implement cutting edge security technology and processes. Access Control is obviously going to be critical to securing the PII as are the processes around backing up, handling and responding to incidents.
How to secure PII?
As mentioned in earlier weeks, a good starting place is the implementation of an Information Security Management System such as ISO27001. If your organisation has, or is in the process of achieving 27001 certification, then you have pretty much nailed this area. If not, then take a look at it. You need to be:
* Adopting an information security policy such as 27001 and understanding what needs to be done to meet it in your organisation
* Developing a thorough understanding of the data being processed and implementing appropriate physical security controls
* Have a well documented access management process in place
* Develop and regularly test a Business Continuity plan – not just a DR plan which tends not to include the wider business stakeholders
* Have a documented incident detection and investigation process in place to address security incidents
The security of PII is often thrown over to IT to sort out, but that will not be enough to meet GDPR expectations. The whole business, right from the top, need to understand and support the processes to ensure end-to-end protection. Any fines will be applied to the business as a whole – therefore prevention needs to be an organisation wide responsibility. If your organisation still feels that one department should make this problem go away, then your starting point may be a conversation with senior management explaining what GDPR is and who is going to suffer if things go wrong. That may help you get the required support.
Summary of Securing PII
This section is all about process implementation. Everything from Security Policies, Segregation of Duties, Background Checks, Access Controls, Business Wide Risk Assessments, Asset Inventories, Software Development processes – everything that touches the security of the data that your organisation processes. It needs to be owned by everyone in the organisation, because ultimately everyone will suffer if a breach occurs.
Next week – seven of eight:
Next week we will focus on the organisation changes to be considered as part of GDPR and make sure that the additional communication channels required are met.
Any questions contact about this week or any other GDPR topic, please contact graeme.riley@intersyscompliance.com
Graeme Riley is an experienced Global CIO with extensive experience in IT Security and Data Protection. He is currently a Director at Intersys Compliance Ltd.


